人工智能可以写代码,但技能可以保护代码。
我们的企业安全编码平台培养了在不减缓交付速度的情况下保护人工和人工智能生成的代码所需的技能。












































传统的安全培训侧重于 — 不是能力。静态扫描会在问题出现后检测到问题。 降低软件风险需要改善安全编码行为 安全编码能力是有效的人工智能软件治理的基础。
Build developer capability for secure AI development
Secure Code Warrior Learning provides AI security training that builds the skills behind every commit. Developers learn to secure AI-generated code through hands-on practice across real-world AI workflows, reducing risk at the source.
大规模建立安全编码能力
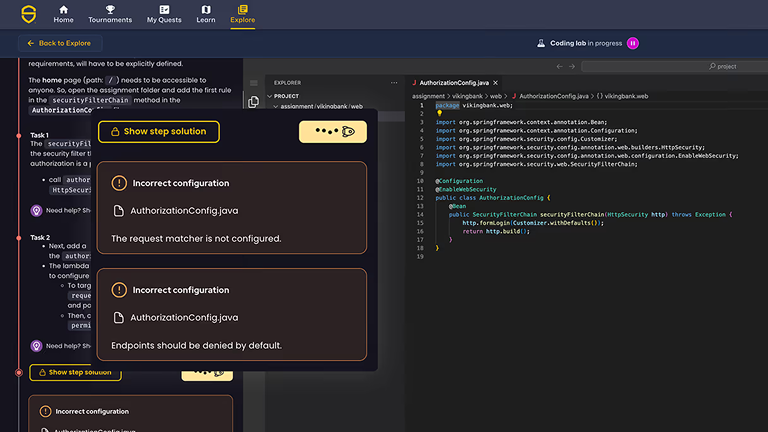
动手安全编码实验室
开发人员通过涵盖 75 多种语言和框架的交互式练习来解决实际漏洞。
特定于 AI 的安全模块
验证和保护 AI 生成的代码,检测不安全模式,并在 AI 辅助工作流程中应用安全标准。
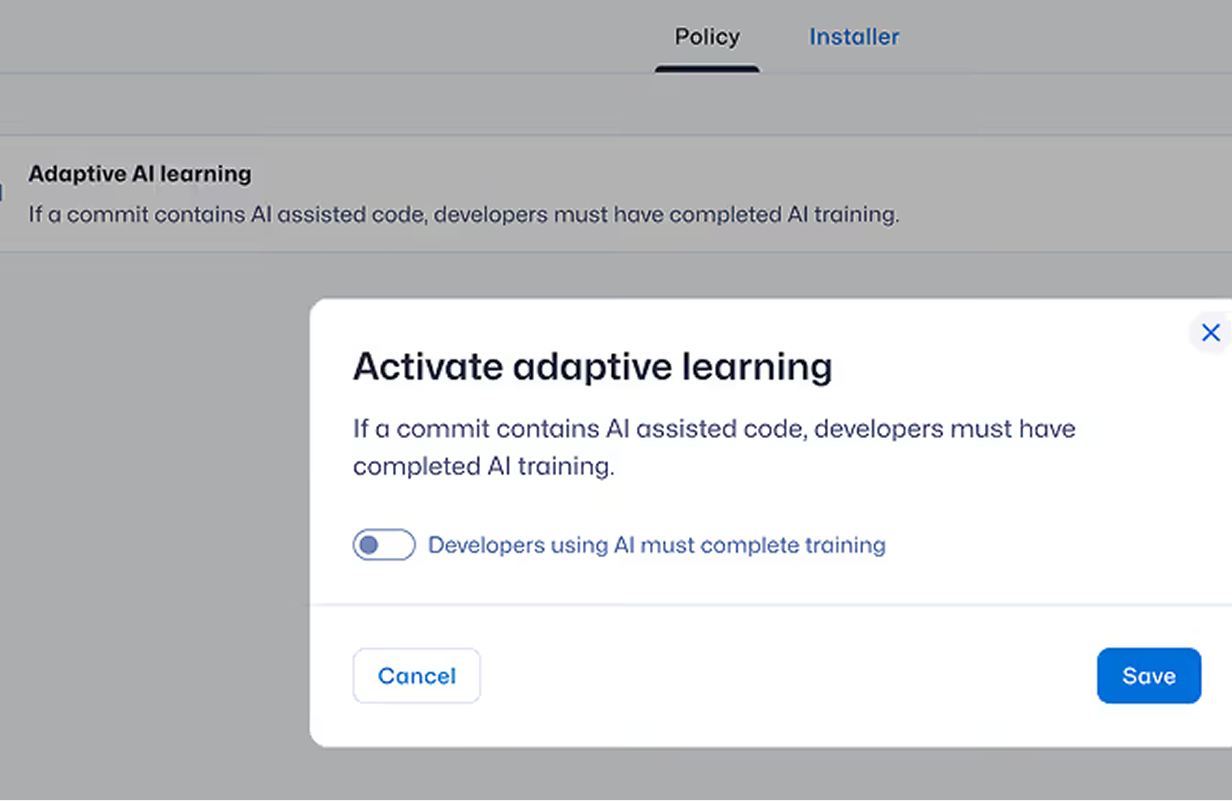
自适应学习路径
根据开发者行为、提交风险信号或基准测试差距自动分配有针对性的培训。
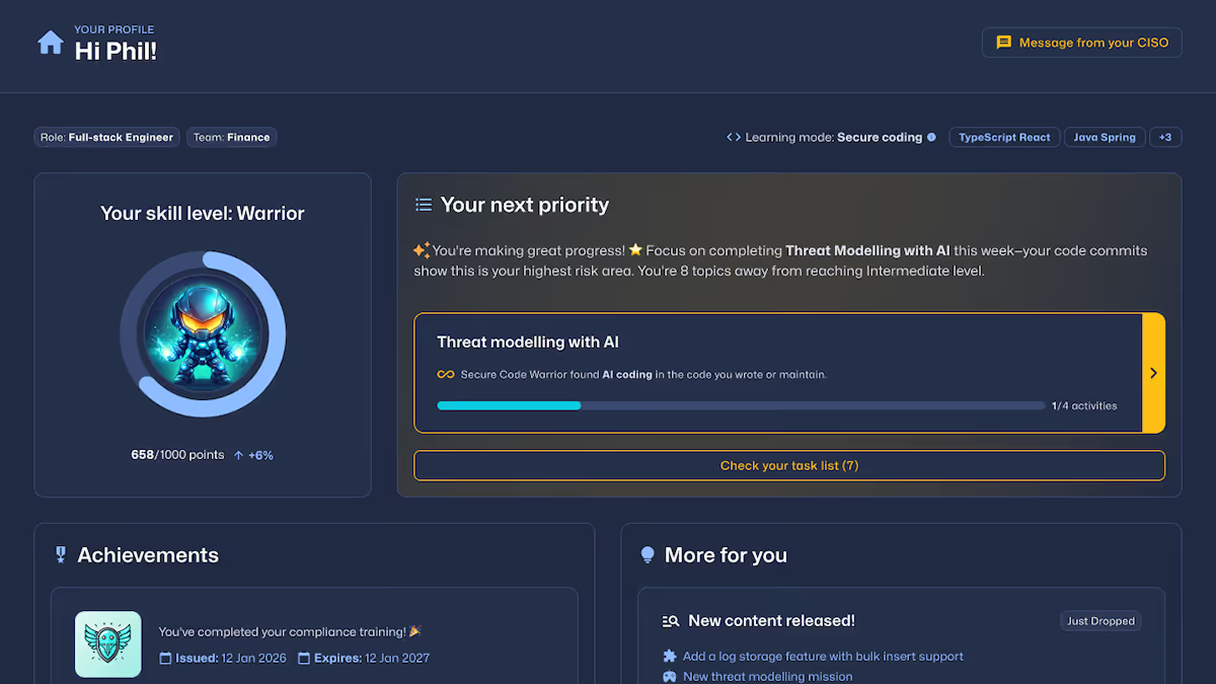
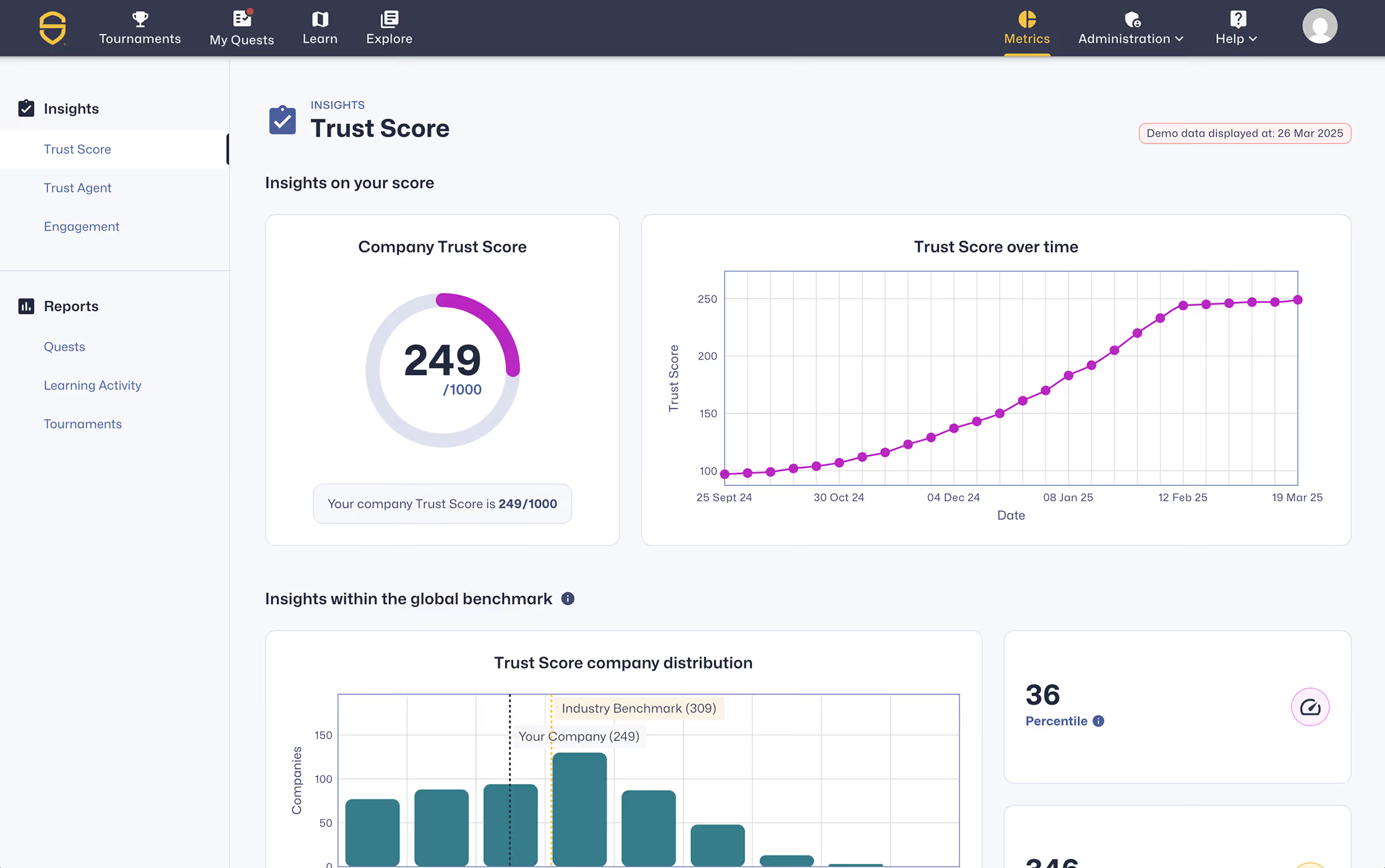
衡量进度
使用 SCW Trust Score® 评估开发人员熟练程度,与同行进行基准测试,并跟踪可衡量的安全编码进度。
Assurer la conformité
将培训与 OWASP 前十名、NIST、PCI DSS、CRA 和 NIS2 相结合,并提供可供审计的报告。
Contrôle de la surface de développement alimenté par l'intelligence artificielle
Rendre le développement alimenté par l'intelligence artificielle visible, sécurisé et résilient, prévenir les vulnérabilités avant la mise en production, afin que les équipes puissent agir rapidement et en toute confiance.
Quêtes
Laboratoires de codage
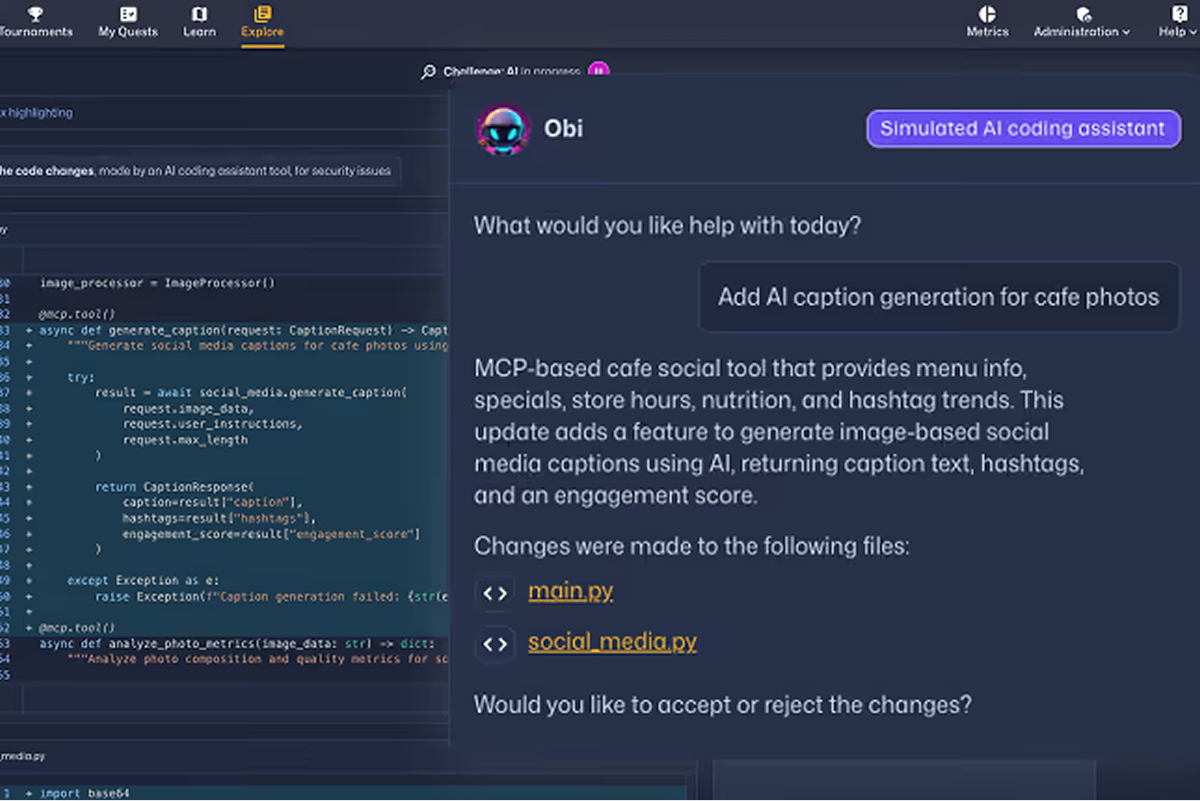
Les défis de l'IA
Check out the SCW Learning Content Guide which outlines the breadth and depth of training available across the Secure Code Warrior platform, including secure coding vulnerabilities, AI security topics, programming languages, frameworks, and role-based learning paths.
Missions
Réduire les vulnérabilités à la source
Secure Code Warrior Learning 减少了反复出现的漏洞,增强了安全编码习惯,并展示了可衡量的开发这些结果表明,企业安全编码培训在现代开发环境中大规模产生了可衡量的影响。




是时候修复了
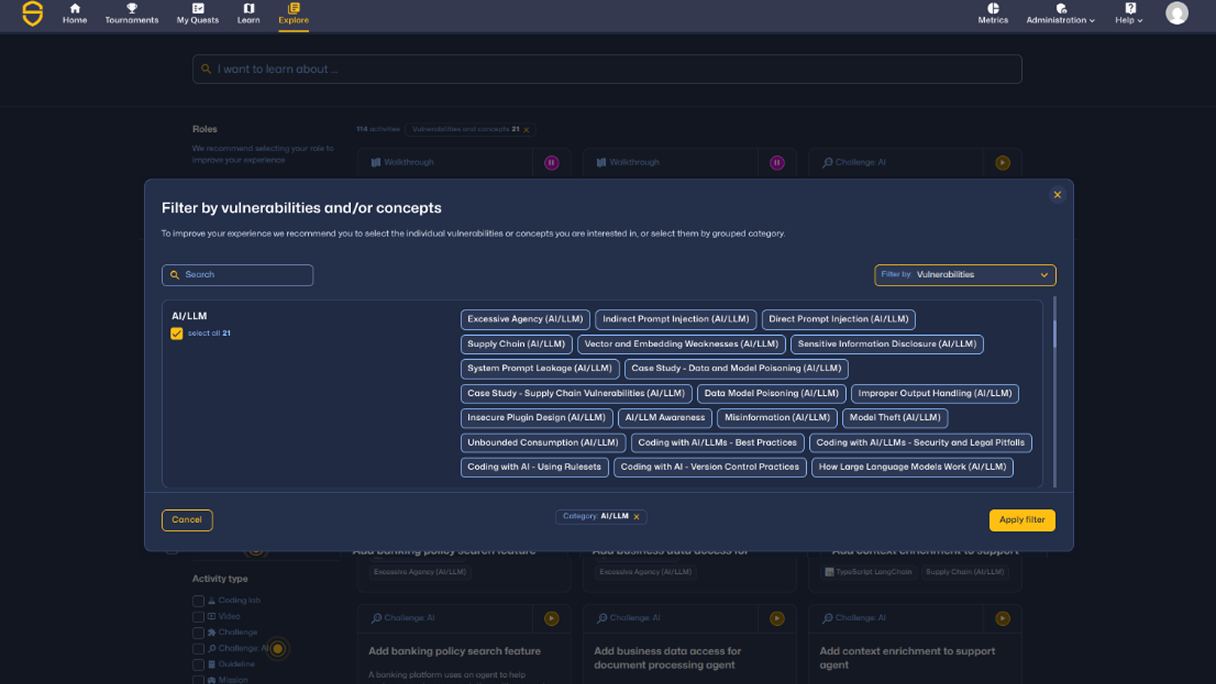
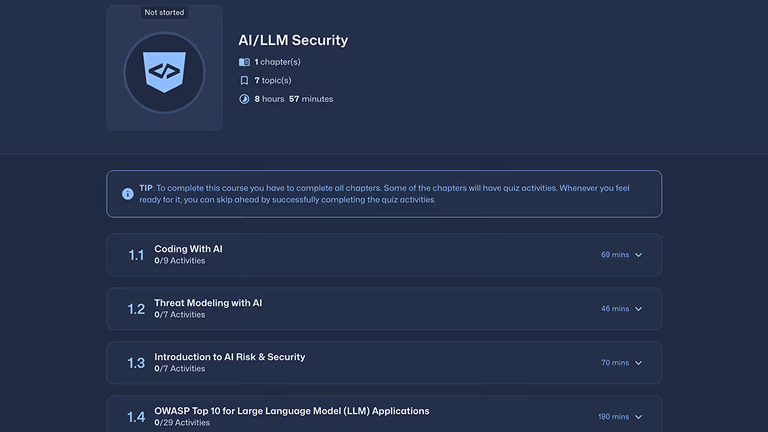
What developers learn in AI security training
Coverage spans LLM vulnerabilities, agent protocols, infrastructure security, and foundational AI security design — mapped to real developer workflows.
Practice real-world AI and LLM security risks.
AI security training teaches developers how to identify, prevent, and remediate vulnerabilities in AI-generated code and modern AI systems, including:
Build foundational AI security knowledge
Developers learn how to securely design and review AI systems through:
Secure AI agents, protocols, and cloud AI environments
Understand and mitigate risks across agent-based systems and AI infrastructure, including MCP and cloud AI services:
Secure AI services and model integrations
Model Context Protocol — Secure AI agents and protocol interactions
专为 AI 治理团队打造
展示可衡量的开发人员能力,降低人工和人工智能辅助开发中的软件风险。
安全代码始于安全的开发人员
增强安全编码技能,减少引入的漏洞,并在整个组织中建立可衡量的开发人员信任。
通过动手安全编码学习减少漏洞
了解 Secure Code Warrior 如何提高开发人员安全技能、减少漏洞并实现可衡量的风险降低。